Automating Regulatory Compliance with Security Reporting and Remediation
Key Takeaways
- Manual compliance programs are failing under the weight of evolving frameworks, distributed infrastructure, and resource constraints
- Continuous monitoring replaces point-in-time assessments, providing real-time control visibility across hybrid and multicloud environments
- Automated reporting transforms audit readiness from a time-intensive project into a continuous operational state
- Security remediation closes the compliance loop, enabling consistent, immediate resolution of policy violations
- Platform selection determines success — true compliance automation requires unified visibility, multi-framework mapping, and hybrid multicloud coverage
The Case for Continuous Compliance Automation
Enterprise IT teams operate under mounting compliance pressure. Regulatory frameworks like HIPAA, PCI-DSS, NIST 800-53, and SOC 2 continue to evolve, each demanding stricter controls and more comprehensive documentation. At the same time, infrastructure has grown exponentially more distributed, spanning on-premises data centers, private clouds, public cloud providers, and edge locations. Yet compliance teams remain lean, often managing these expanding requirements with the same headcount they had five years ago.
Manual compliance programs are breaking under this pressure. Audit preparation stretches into weeks-long sprints as teams scramble to collect evidence from disconnected systems. Remediation queues age as security engineers work through spreadsheets of findings, prioritizing based on incomplete context. Point-in-time assessments create a dangerous illusion of readiness, passing controls one quarter while violations accumulate silently the next.
According to IBM’s 2025 Cost of a Data Breach Report, organizations with extensive AI and automation capabilities reduced breach costs by $1.9 million on average compared to those without automation. When compliance workflows still rely on manual data collection, human error becomes inevitable — and response times stretch from hours to days, widening the financial and operational blast radius of every incident.
Automation isn’t just an efficiency gain — it’s the foundation for maintaining continuous compliance in modern distributed environments.
What is Compliance Automation?
Compliance automation is software and integrated tooling that continuously monitors, reports on, and remediates security and policy controls across enterprise infrastructure without requiring manual data collection. It transforms compliance from an episodic assessment cycle into a real-time operational capability.
What Compliance Automation Means in Modern Enterprise IT
True compliance automation differs fundamentally from basic periodic scanning. It’s built on three operational pillars: continuous evidence collection, real-time control visibility, and automated or guided remediation.
Traditional compliance tools take snapshots by running scans on a schedule, generating reports at fixed intervals, and leaving organizations blind to what happens between checks. Compliance automation operates continuously, monitoring infrastructure state, collecting evidence automatically, and surfacing policy violations as they occur rather than weeks later.
The challenge intensifies in hybrid and multicloud environments. A security control might pass validation in your on-premises vCenter cluster while simultaneously failing in AWS, Azure, or edge locations. Network segmentation policies enforced consistently in one environment may not even exist in another. Without unified visibility and enforcement, compliance becomes a patchwork of disconnected point solutions, each monitoring a subset of infrastructure while blind spots persist.
Nutanix approaches this challenge by providing policy consistency and operational visibility across distributed environments from a unified layer. Rather than deploying separate compliance tools for each infrastructure surface, the Nutanix platform extends security controls and compliance monitoring from core infrastructure through edge deployments.
Cloud automation becomes the mechanism that translates compliance requirements into infrastructure state by defining controls once, enforcing them everywhere, and maintaining continuous validation across the entire hybrid stack.
Why Security Reporting is the Foundation of Compliance Automation
Security reporting transforms raw infrastructure telemetry into actionable compliance intelligence. Without effective reporting, even the most comprehensive monitoring generates noise rather than insight. Automated compliance reporting provides four critical capabilities:
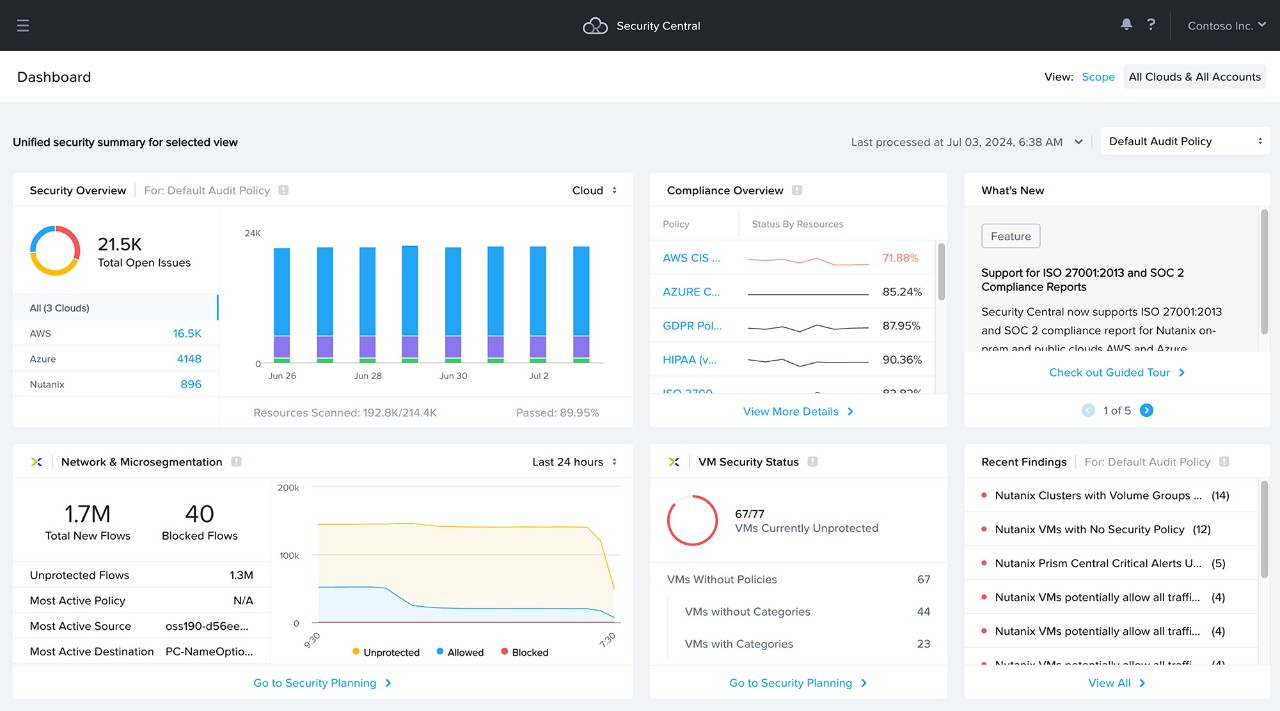
Unified control status visibility
Aggregated control status across all environments appears in centralized, real-time dashboards. Rather than logging into separate consoles for VMware, AWS, Azure, and Kubernetes to piece together compliance posture, teams see holistic control coverage from a single interface. When a firewall rule changes in one environment or a certificate expires in another, unified visibility surfaces the compliance impact immediately.
Continuous audit trails
Timestamped, tamper-resistant evidence records cut audit preparation time from weeks to hours. Every configuration change, policy enforcement action, and control validation generates an audit entry automatically. When auditors request evidence of continuous encryption enforcement or network segmentation compliance, teams provide complete, chronological records rather than reconstructing events from disconnected logs.
PwC’s 2025 Global Compliance Survey shows that rising regulatory complexity and disconnected data flows are putting unprecedented pressure on compliance teams, with 71% of organizations planning digital‑transformation initiatives that require compliance support. Manual evidence collection becomes a natural choke point in this environment — and automated audit trails eliminate that bottleneck entirely.
Exception reporting
Exception reporting surfaces failing and at-risk controls before they become audit findings. Rather than discovering violations during scheduled assessments, teams receive immediate alerts when controls drift out of compliance. A VM deployed without encryption, a network segment created outside policy boundaries, or a privileged account granted without approval all trigger automated exception reporting with full context.
Executive visibility
Role-appropriate dashboards provide CIOs and board-level stakeholders with compliance posture summaries without overwhelming them with operational detail. Executives see framework-specific readiness scores, trending violation counts, and mean time to remediation metrics that translate security operations into business risk indicators.
Nutanix Security Central serves as the unified platform enabling this visibility, aggregating compliance telemetry from across distributed infrastructure and presenting it through role-optimized interfaces.
How Automated Remediation Supports Continuous Compliance
Automated remediation is what closes the detection-to-resolution loop and transforms compliance from episodic to continuous. Detection alone doesn’t maintain compliance — rapid, consistent remediation does.
Effective automated remediation systems handle lower-risk issues immediately and route higher-risk findings to the appropriate team with complete context. When a VM is deployed without required encryption, the system either applies encryption automatically or generates a structured ticket containing the VM identifier, policy requirement, regulatory framework impact, and recommended remediation steps. Security engineers receive actionable work items rather than alerts requiring investigation.
The operational gap between manual and automated remediation is stark. A detected failure in a manual workflow enters a queue, waits for triage, undergoes priority assignment, gets assigned to an engineer, and then awaits remediation — a process spanning days or weeks. Automated remediation closes that window consistently, every time.
"When configurations drift from approved baselines, automated remediation should restore them to the correct state without waiting for human intervention. This shift from periodic auditing to continuous enforcement transforms compliance from a checkbox into an operational advantage."
— Nutanix, "The Sovereign Edge: The Next Enterprise Control Plane"
Nutanix Flow demonstrates this principle through microsegmentation and policy enforcement. Network security policies are defined once and enforced consistently across VMs, containers, and cloud workloads. When application teams deploy new workloads, Flow applies appropriate microsegmentation automatically rather than waiting for manual firewall rule implementation. Compliance becomes an inherent property of infrastructure rather than a post-deployment remediation requirement.
What an End-to-End Compliance Automation Workflow Looks Like
A complete compliance automation workflow spans six stages, operating continuously rather than as a periodic cycle:
Detection
Continuous, real-time monitoring runs across on-premises infrastructure, private clouds, and public cloud providers rather than relying on scheduled scans executed weekly or monthly. Every configuration change, policy modification, and workload deployment triggers immediate control validation against defined compliance frameworks.
Reporting
Auto-logged findings include complete context: what failed, where it failed, when it failed, and which regulatory frameworks are impacted. Compliance dashboards and evidence records update immediately rather than waiting for batch report generation. Engineers and auditors see the same real-time data without synchronization delays.
Prioritization
Findings receive automated scoring based on severity, framework impact, and blast radius. A failed encryption control affecting customer data in a HIPAA-regulated environment receives higher priority than a documentation gap in a development cluster. High-priority issues surface immediately through automated escalation rather than waiting for manual triage.
Remediation
Predefined automated responses handle known issue types immediately. Encryption violations trigger automatic policy application, unauthorized network connections are blocked, and expired certificates generate renewal workflows. Complex findings that require human judgment generate structured, pre-triaged tickets with recommended actions and rollback procedures.
Validation
Systems verify control restoration automatically without manual confirmation. When automated remediation applies an encryption policy, the validation stage confirms that targeted resources now meet compliance requirements and updates control status accordingly. Failed remediation attempts trigger escalation rather than appearing as resolved work items.
Evidence update
Compliance records update automatically with timestamps, operator attribution, and validation status. Evidence collection becomes a byproduct of normal operations rather than a separate audit preparation activity. When auditors request proof of continuous compliance, teams export complete evidence packages covering the entire assessment period.
Nutanix Cloud Manager (NCM) serves as the operational layer connecting infrastructure state to compliance outcomes, orchestrating remediation workflows across distributed environments and maintaining unified evidence records.
Common Gaps in Manual or Partially Automated Compliance Programs
Most organizations don’t start with comprehensive compliance automation and instead evolve gradually from spreadsheets and point solutions. This creates programs that appear complete but contain critical gaps:
Evidence gaps between audit cycles — Point-in-time assessments provide quarterly or annual snapshots while violations occur continuously, leaving organizations blind to compliance drift between formal reviews
Inconsistent remediation across environments — AWS resources are remediated using cloud-native tools, on-premises infrastructure relies on manual procedures, and Kubernetes clusters follow different workflows, creating inconsistent security posture
Framework sprawl as regulatory requirements multiply — Organizations manage separate control sets for SOC 2, HIPAA, PCI-DSS, and NIST, collecting redundant evidence for overlapping requirements
Slow mean time to resolution due to manual queues — Findings enter ticketing systems, undergo manual prioritization, wait for engineer availability, and age in remediation queues while risk accumulates
Audit preparation as a time-consuming project — Teams spend weeks collecting evidence, reconciling control status across systems, and generating compliance reports rather than maintaining continuous audit readiness
Who Benefits from Automated Compliance Management and How
Compliance automation delivers distinct value to different stakeholder roles:
CIOs gain executive dashboards that translate infrastructure security posture into quantified business risk. Rather than receiving operational security reports requiring translation, CIOs see framework-specific compliance scores, control coverage percentages, and trending metrics that inform strategic risk decisions. Automation also reduces overall program costs by eliminating manual evidence collection and streamlining audit cycles.
IT Managers experience dramatic reductions in manual effort and operational toil. Hours previously spent gathering evidence for audit submissions, reconciling control status across disconnected systems, and managing spreadsheet-based compliance tracking are reclaimed for strategic initiatives. Automated workflows also eliminate human error in evidence collection and remediation execution.
Cybersecurity Officers achieve continuous control coverage with real-time deviation detection rather than discovering violations during quarterly assessments. When security controls drift out of policy, automated systems detect and remediate immediately instead of allowing risk to accumulate between assessment cycles. This shift from reactive to proactive compliance fundamentally changes security operations.
Compliance Officers maintain always-ready evidence repositories and multi-framework policy mapping that eliminates redundant control validation. A single infrastructure control maps to requirements in HIPAA, SOC 2, NIST 800-53, and PCI-DSS simultaneously, with evidence collected once and applied across all frameworks. Audit preparation transforms from a major project to a simple evidence export.
The next generation of virtual networking and security enables this unified approach by embedding compliance capabilities directly into infrastructure rather than layering them on through external tools.
Key Capabilities to Look for in Compliance Automation Software
When evaluating compliance automation platforms, enterprise teams should prioritize six essential capabilities:
Continuous control monitoring — Real-time validation rather than periodic scanning. Infrastructure changes trigger immediate control assessment, not scheduled batch checks that create compliance blind spots.
Centralized visibility — Single-pane-of-glass dashboards spanning all infrastructure. Teams view compliance posture across VMware, AWS, Azure, Kubernetes, and edge environments from unified interfaces rather than context-switching between disconnected tools.
Multi-framework policy mapping — Individual controls map to requirements across multiple regulatory frameworks simultaneously. Organizations validate encryption controls once and demonstrate compliance with HIPAA encryption requirements, SOC 2 logical access controls, and NIST 800-53 cryptographic protection controls from the same evidence.
Automated evidence collection — Complete audit trails generated as a byproduct of normal operations. No manual log exports, screenshot collection, or evidence compilation required, as compliance systems automatically maintain tamper-resistant evidence repositories.
Remediation triggers and workflow orchestration — Automated responses for known issue patterns combined with structured human workflows for complex findings. Low-risk violations are resolved automatically while high-risk issues route to appropriate teams with complete triage context.
Hybrid multicloud coverage — Infrastructure-native compliance rather than agent-based bolt-ons. Controls are enforced at the infrastructure layer and validated continuously across on-premises data centers, private clouds, public cloud providers, and edge locations.
Explore how Nutanix Flow delivers these capabilities through unified policy enforcement and continuous compliance validation.
Compliance automation uses software to continuously monitor, report on, and remediate security controls across enterprise infrastructure without manual intervention. It transforms compliance from periodic assessments into real-time operational capabilities.
Automated reporting maintains continuous evidence collection rather than requiring manual preparation before audits. When auditors request evidence, teams export complete, timestamped records covering the entire assessment period rather than reconstructing events from disconnected logs.
Traditional compliance relies on point-in-time assessments, using periodic scans that validate controls on a schedule but leave organizations blind between checks. Continuous compliance automation monitors infrastructure continuously, detects violations immediately, and maintains real-time compliance posture visibility.
Remediation closes the loop between detection and resolution. Without automated remediation, detected violations accumulate in manual queues while risk persists. Automated remediation resolves lower-risk issues immediately and routes complex findings to appropriate teams with complete context.
Yes, effective compliance automation platforms provide infrastructure-native visibility across on-premises data centers, private clouds, public cloud providers, and edge locations. Controls are defined once and enforced consistently across all infrastructure surfaces rather than requiring separate tools for each environment.
©2026 Nutanix, Inc. All rights reserved. Nutanix, the Nutanix logo and all Nutanix product and service names mentioned are registered trademarks or trademarks of Nutanix, Inc. in the United States and other countries. All other brand names mentioned are for identification purposes only and may be the trademarks of their respective holder(s).