Securing EUC for Protection from Ransomware and Malware
The COVID-19 pandemic, has required IT teams to rapidly develop and deploy new remote work solutions. Big changes have occurred—possibly with only cursory thought to increased cyber risks. A recent article in MIT Sloan Management Review discussed five new risk factors that IT professionals should be aware of:
- A 3-4x increase in daily cybersecurity complaints
- Expanded attack surface due to vulnerabilities in remote work technologies
- Distracted workforces susceptible to phishing and other attacks
- Unanticipated staff shortages stalling and reducing threat response
- IT and security staff may be coping with multiple crises simultaneously
The CyberArk Remote Work Survey noted that “40% of organizations have not increased their security protocols despite the significant change in the way employees connect to corporate systems and the addition of new productivity applications.” Perhaps it’s time to revisit the security of your work from home (WFH) solutions.
EUC Improves WFH Security
End User Computing (EUC)—including virtual desktop infrastructure (VDI) and Desktop as a Service (DaaS)— helps improve WFH security by eliminating the need to store critical data on endpoint devices that can be easily lost, stolen, or compromised. Instead, users access data from a centralized, enterprise-class datacenter where it is professionally managed, monitored, and backed up.
Research conducted by Enterprise Strategy Group (ESG), shows security is now the paramount concern for those looking for an EUC solution. Centralizing data is not enough by itself to protect your organization from ransomware, malware, and other now-pervasive cyber threats.
Nutanix: Superior Security for EUC
At Nutanix, we have a proven track record of delivering secure, easy-to-manage EUC solutions. The Nutanix platform is hardened and secure by design, with multiple layers of security to protect your EUC environment:
- Infrastructure. Nutanix adheres to industry standards and best practices, with built-in auditing and remediation to reduce configuration drift and correct operator errors that inadvertently open the door to a breach.
- Data. Data-at-rest encryption combined with least-privilege access, role-based access control (RBAC), and multi-factor authentication (MFA) reduce the risk that critical data is exposed.
- Network Security. Advanced microsegmentation enables software-defined network, application, and identity-based segmentation for a Zero Trust approach.
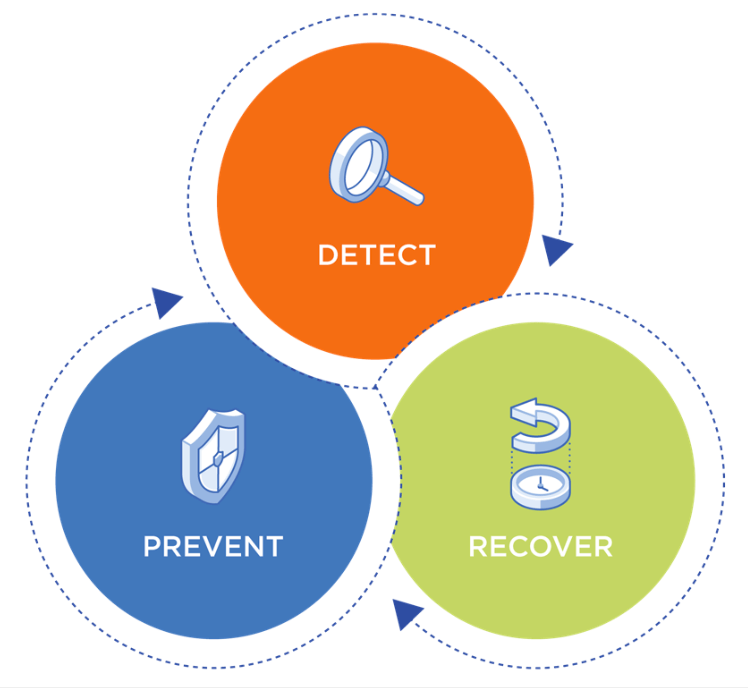
- Ransomware prevention and protection. Nutanix enables advanced ransomware protection via its business continuity and disaster recovery (BCDR) solutions.
Are You Protected?
If you’re deploying or planning to implement an EUC solution, security should be a top consideration. Our technical brief, EUC Security for Work-from-Home describes the capabilities, industry best practices, and techniques to incorporate into your EUC strategy, including an explanation of Nutanix security technologies and how to use them.
© 2020 Nutanix, Inc. All rights reserved. Nutanix, the Nutanix logo and all Nutanix product and service names mentioned herein are registered trademarks or trademarks of Nutanix, Inc. in the United States and other countries. All other brand names mentioned herein are for identification purposes only and may be the trademarks of their respective holder(s). This press release may contain links to external websites that are not part of Nutanix.com. Nutanix does not control these sites and disclaims all responsibility for the content or accuracy of any external site. Our decision to link to an external site should not be considered an endorsement of any content on such a site. Certain information contained in this post may relate to or be based on studies, publications, surveys and other data obtained from third-party sources and our own internal estimates and research. While we believe these third-party studies, publications, surveys and other data are reliable as of the date of this post, they have not independently verified, and we make no representation as to the adequacy, fairness, accuracy, or completeness of any information obtained from third-party sources.
This post may contain express and implied forward-looking statements, which are not historical facts and are instead based on our current expectations, estimates and beliefs. The accuracy of such statements involves risks and uncertainties and depends upon future events, including those that may be beyond our control, and actual results may differ materially and adversely from those anticipated or implied by such statements. Any forward-looking statements included herein speak only as of the date hereof and, except as required by law, we assume no obligation to update or otherwise revise any of such forward-looking statements to reflect subsequent events or circumstances.